Northstrix
Member
Hello, everyone.
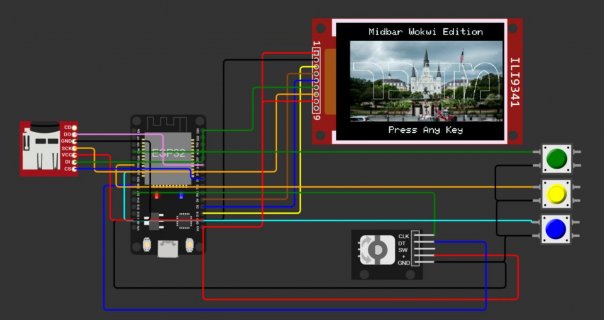
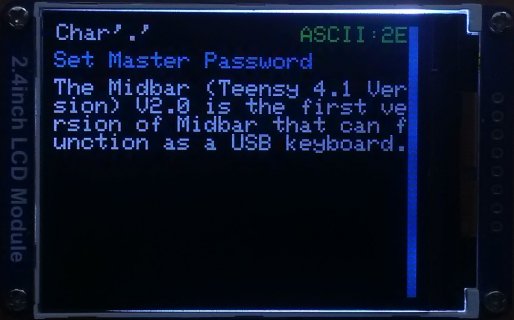
Let me announce that the Midbar (Teensy 4.1 Version) V2.0 is out.
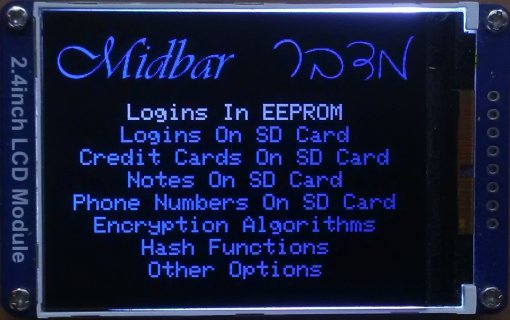
That version of Midbar combines in it the password vault, credit card vault, phone number vault, note vault, data encryptor/decryptor, and data hasher.
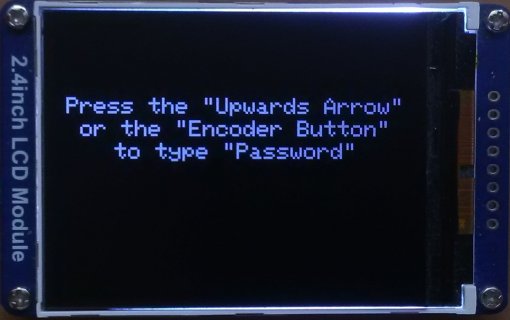
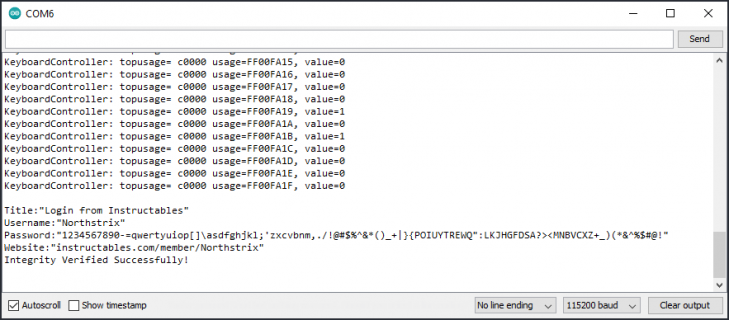
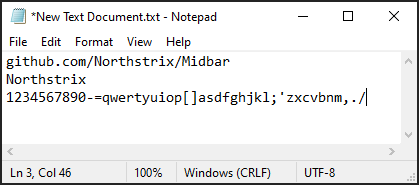
Aside from the fact that this is the first version of Midbar that can function as a USB keyboard, it also comes with lots of convenient features, such as:
Midbar (Teensy 4.1 Version) V2.0 can be used without the SD card. Although without the SD card, you would only have 16 slots available for your login credentials, you can still use it as a data encryptor/decryptor and data hasher;
And let's not forget that this version of Midbar allows you to encrypt an arbitrary string with a length of up to 10 000 characters using the 3DES + AES + Blowfish + Serpent Encryption Algorithm in the cipher block chaining mode of operation combined with the HMAC-SHA256 without any problems.
If you're interested in the Midbar (Teensy 4.1 Version) V2.0, you can find the tutorials for it on:
Instructables: https://www.instructables.com/Midbar-Teensy-41-Version-V20/
Hackster: https://www.hackster.io/northstrix/midbar-teensy-4-1-version-v2-0-344682
Medium: https://medium.com/@Northstrix/midbar-teensy-4-1-version-v2-0-f5e17c241894
As for the firmware, the links are in the tutorials. But for the sake of convenience, I paste the part with the links here:
You can download the firmware for Midbar from one of these sources.
SourceForge: https://sourceforge.net/projects/midbar/
GitHub: https://github.com/Northstrix/Midbar
If you just need the firmware for the device alongside the RNG, then I would advise you to download a 0.2 MB archive from SourceForge.
But if you need the firmware for all versions of Midbar alongside the extra code, photos, and diagrams, in that case, I would advise you to download the 199 MB archive from GitHub.
I hope you find this device handy.
Best regards,
Maxim Bortnikov
Let me announce that the Midbar (Teensy 4.1 Version) V2.0 is out.
That version of Midbar combines in it the password vault, credit card vault, phone number vault, note vault, data encryptor/decryptor, and data hasher.
Aside from the fact that this is the first version of Midbar that can function as a USB keyboard, it also comes with lots of convenient features, such as:
- USB keyboard support - Allows you to interact with Midbar using the USB keyboard connected to the Teensy 4.1 USB port;
- RFID-lockable (four RFID cards + master password to be exact) - This version of Midbar is locked with a combination of four RFID cards and a master password (Not a new feature for the Midbar project itself, but kinda new for the Teensy version of Midbar);
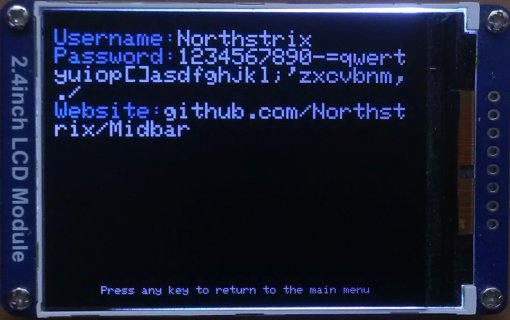
- Combination of EEPROM and SD card storage - Enables you to store 16 login credentials in Teensy's EEPROM and allows you to store as many records on an SD card as there's available space on it (as long as you adjust the value in the "#define MAX_NUM_OF_RECS 999" line of course);
- Ease of data backup - Allows you to effortlessly back up EEPROM data to the SD card or Serial Terminal and restore it just as easily;
- Sophisticated encryption with integrity verification - Midbar utilizes a 3DES + AES + Blowfish + Serpent Encryption Algorithm in the cipher block chaining mode of operation combined with the HMAC-SHA256 to encrypt your data and check its integrity;
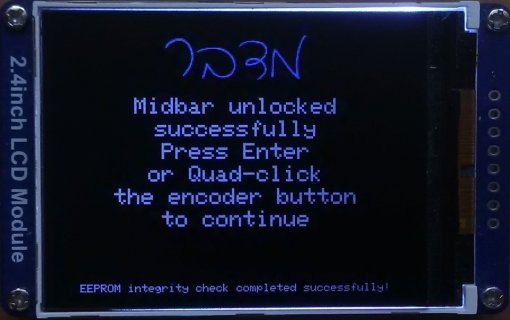
- EEPROM integrity verification - The Midbar checks if the EEPROM is tampered with each time you unlock it;
Midbar (Teensy 4.1 Version) V2.0 can be used without the SD card. Although without the SD card, you would only have 16 slots available for your login credentials, you can still use it as a data encryptor/decryptor and data hasher;
And let's not forget that this version of Midbar allows you to encrypt an arbitrary string with a length of up to 10 000 characters using the 3DES + AES + Blowfish + Serpent Encryption Algorithm in the cipher block chaining mode of operation combined with the HMAC-SHA256 without any problems.
If you're interested in the Midbar (Teensy 4.1 Version) V2.0, you can find the tutorials for it on:
Instructables: https://www.instructables.com/Midbar-Teensy-41-Version-V20/
Hackster: https://www.hackster.io/northstrix/midbar-teensy-4-1-version-v2-0-344682
Medium: https://medium.com/@Northstrix/midbar-teensy-4-1-version-v2-0-f5e17c241894
As for the firmware, the links are in the tutorials. But for the sake of convenience, I paste the part with the links here:
You can download the firmware for Midbar from one of these sources.
SourceForge: https://sourceforge.net/projects/midbar/
GitHub: https://github.com/Northstrix/Midbar
If you just need the firmware for the device alongside the RNG, then I would advise you to download a 0.2 MB archive from SourceForge.
But if you need the firmware for all versions of Midbar alongside the extra code, photos, and diagrams, in that case, I would advise you to download the 199 MB archive from GitHub.
I hope you find this device handy.
Best regards,
Maxim Bortnikov
Attachments
-
 IMG_20230719_184125.jpg312.7 KB · Views: 218
IMG_20230719_184125.jpg312.7 KB · Views: 218 -
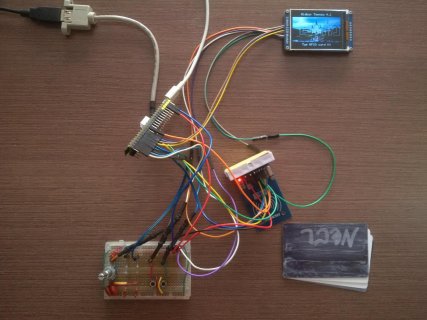 IMG_20230719_184125.jpg155.9 KB · Views: 214
IMG_20230719_184125.jpg155.9 KB · Views: 214 -
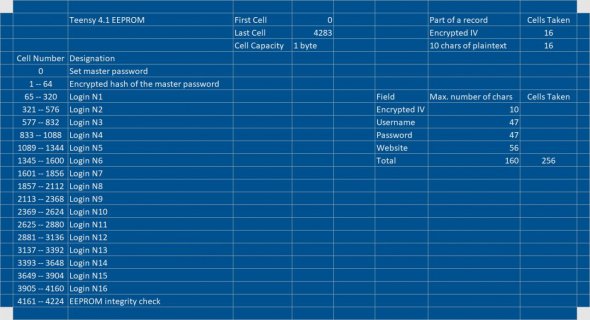 EEPROM Partitioning Table.jpg130.6 KB · Views: 214
EEPROM Partitioning Table.jpg130.6 KB · Views: 214 -
 IMG_20230719_103927.jpg134.6 KB · Views: 213
IMG_20230719_103927.jpg134.6 KB · Views: 213 -
 IMG_20230719_144506.jpg137.2 KB · Views: 201
IMG_20230719_144506.jpg137.2 KB · Views: 201 -
 IMG_20230719_144625.jpg181.3 KB · Views: 182
IMG_20230719_144625.jpg181.3 KB · Views: 182 -
 IMG_20230719_145115.jpg156.1 KB · Views: 189
IMG_20230719_145115.jpg156.1 KB · Views: 189 -
 IMG_20230719_145241.jpg121.2 KB · Views: 200
IMG_20230719_145241.jpg121.2 KB · Views: 200 -
 rec_from_sd_in_ser.png29.5 KB · Views: 188
rec_from_sd_in_ser.png29.5 KB · Views: 188 -
 typed_from_EEPROM.png7.9 KB · Views: 201
typed_from_EEPROM.png7.9 KB · Views: 201