"Maybe it needs certain hardware connected to demonstrate the problem?"
Unfortunately, that is the case.
I only put the stack monitor in after the problem occurred and was suggested by jrraines and luni earlier.
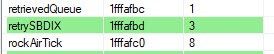
However, once upon a time a while back, I wrote something to analyses the .elf file. In the faulty version, the boolean variable retrySBDIX is allocated 3 bytes:
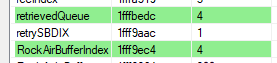
In the working version, retrySBDIX gets 1 byte, as you would expect:
Might this be a problem?
Unfortunately, that is the case.
I only put the stack monitor in after the problem occurred and was suggested by jrraines and luni earlier.
However, once upon a time a while back, I wrote something to analyses the .elf file. In the faulty version, the boolean variable retrySBDIX is allocated 3 bytes:
In the working version, retrySBDIX gets 1 byte, as you would expect:
Might this be a problem?